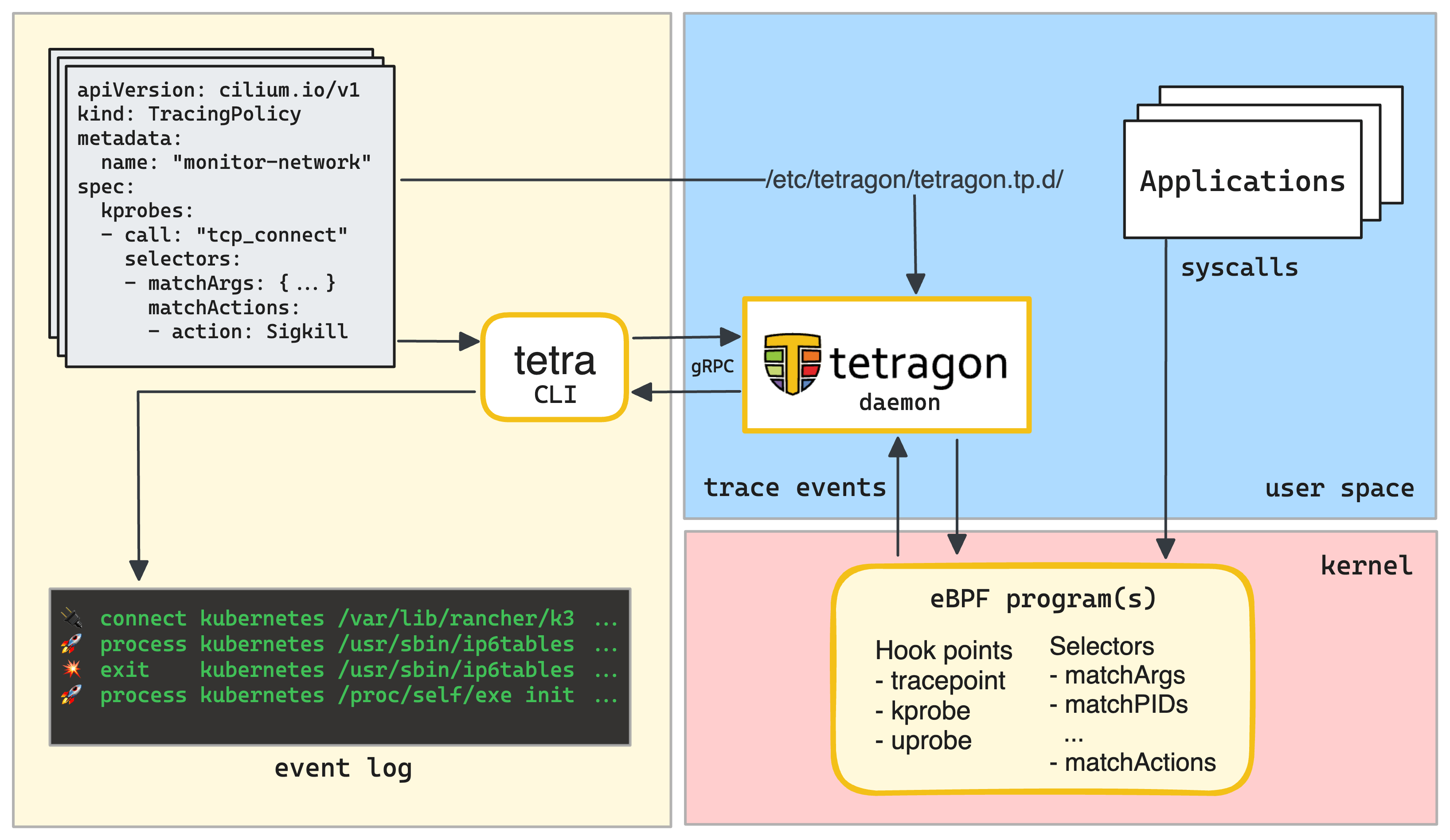
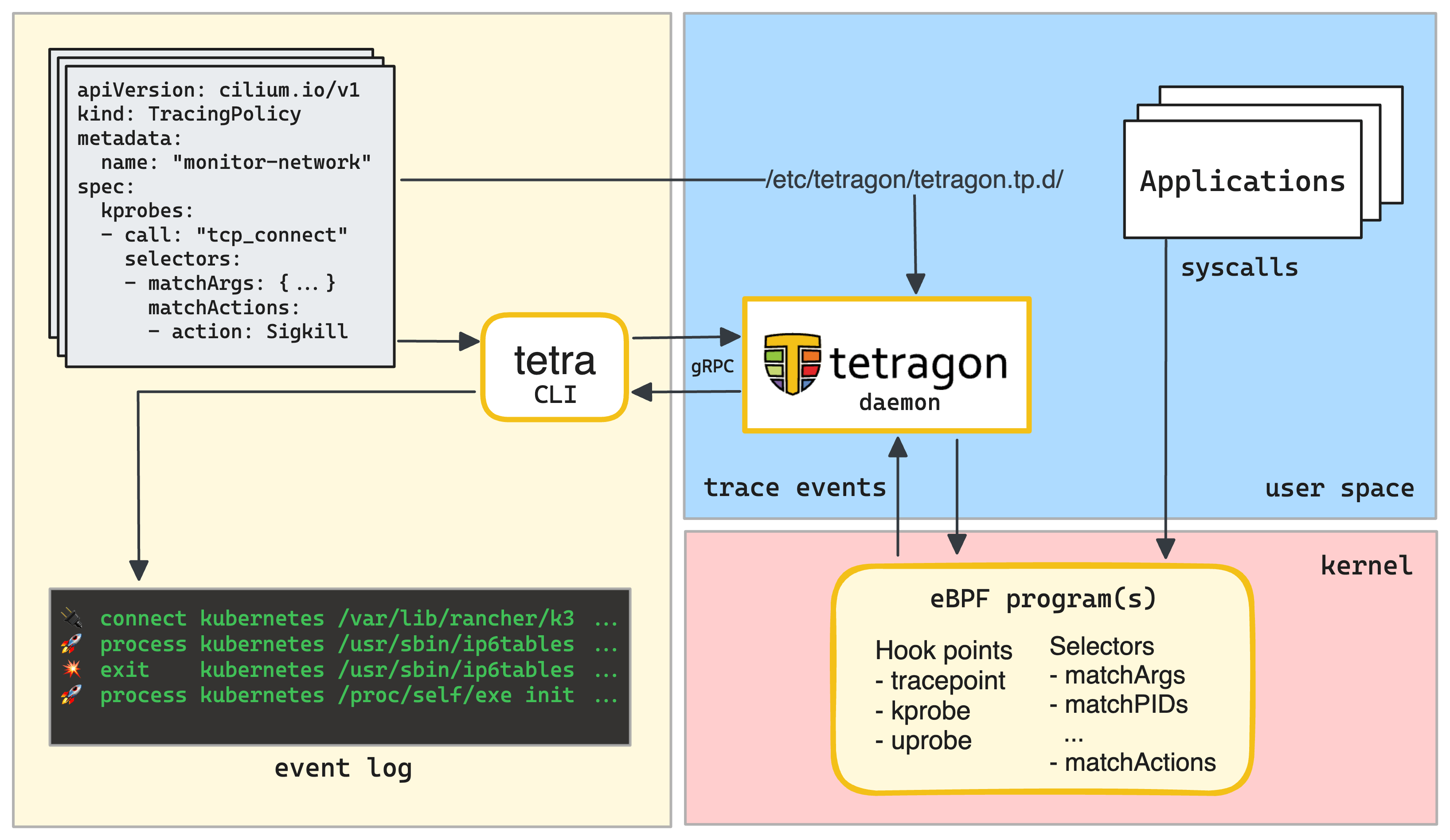
Exploring Tetragon - A Security Observability Tool for Kubernetes, Docker, and Linux
What is Tetragon, how it works, and how to use it to detect and react to security-significant events in your Kubernetes, Docker, or plain Linux environment.
Deep dives into DevOps and Server Side topics where theory blends with hands-on examples. You can try out commands from each tutorial in the attached remote playground, either from the browser or via SSH access from your local terminal — no extra setup required.
Tutorials crafted by iximiuz Labs to help you master DevOps and Server Side topics.
What is Tetragon, how it works, and how to use it to detect and react to security-significant events in your Kubernetes, Docker, or plain Linux environment.
Tutorials from outstanding independent authors proudly hosted by iximiuz Labs.
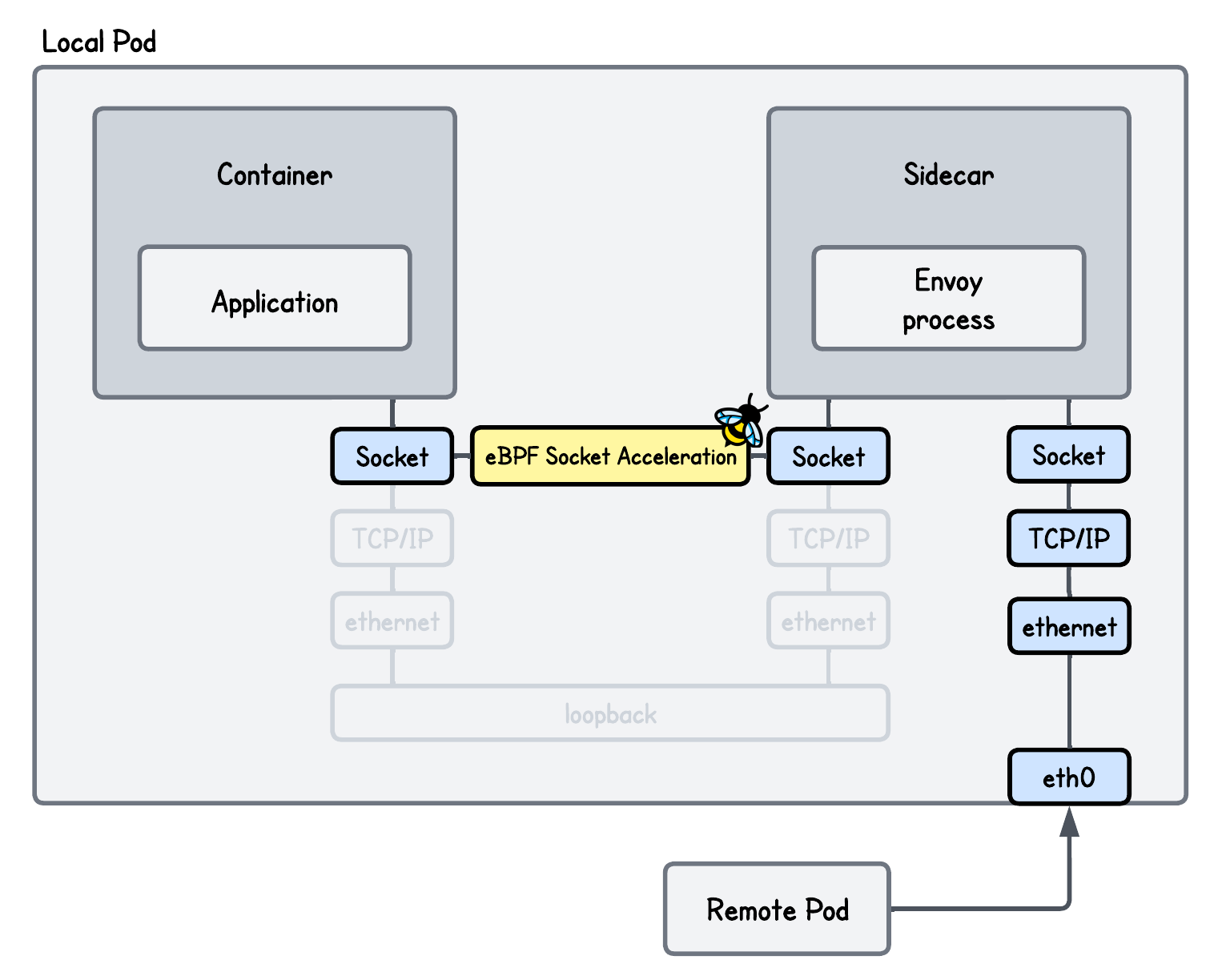
This lab teaches you how to use eBPF socket acceleration to optimize a transparent Envoy proxy setup. You will implement mechanisms that bypass parts of the kernel networking stack to directly transfer data between sockets, improving throughput and reducing latency.
This lab shows how to use eBPF to transparently redirect inbound traffic through an Envoy proxy on the server side, without modifying the application or client. You’ll learn how eBPF can intercept and restore connections so the service remains unaware of the proxy in the network path.
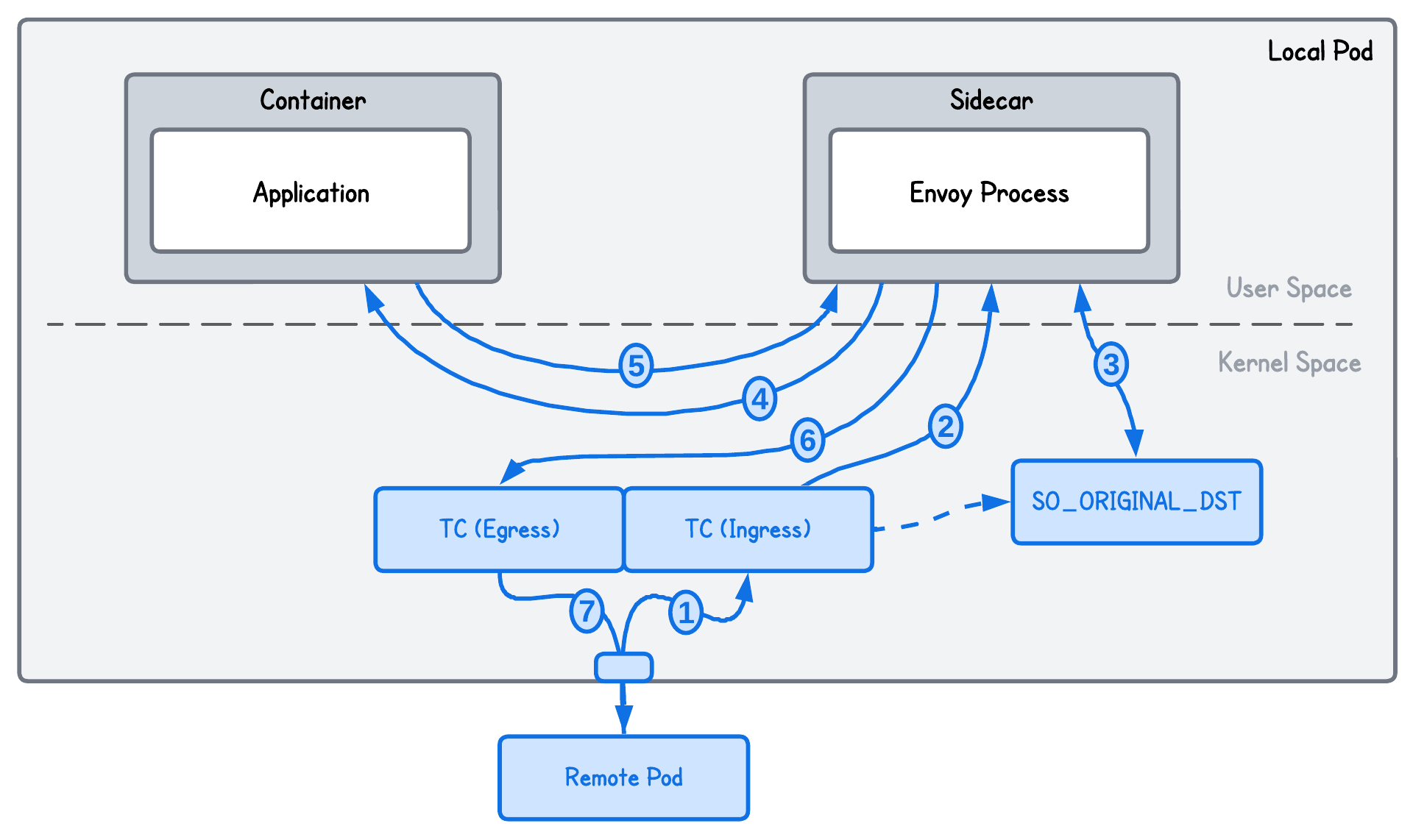
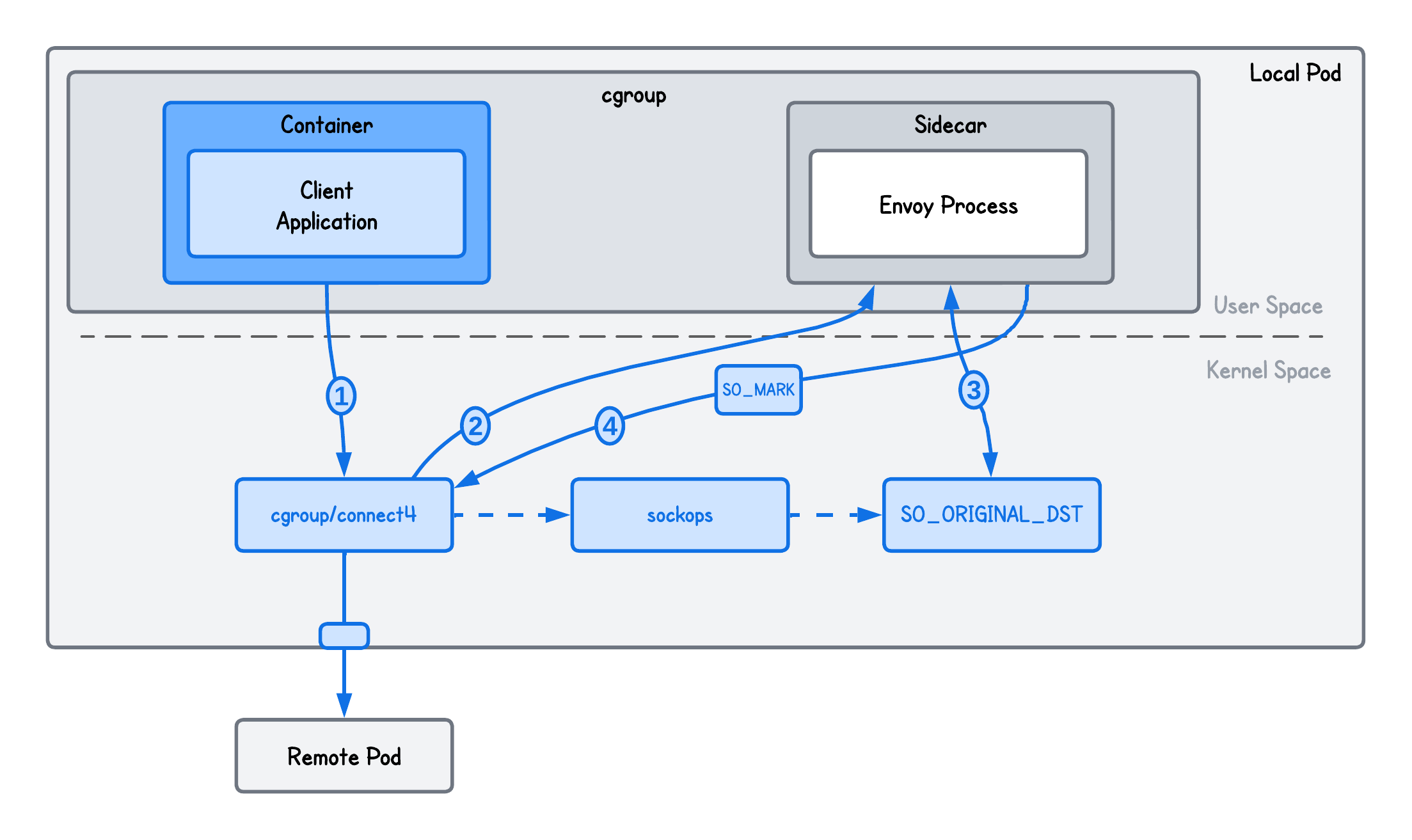
This lab teaches you how to use eBPF to transparently intercept and redirect a client's outgoing traffic to an Envoy proxy without requiring any changes to the application code. You will build a system that recovers original connection metadata via socket-level hooks and uses SO_MARK to prevent infinite routing loops, replacing traditional, complex iptables rules with a high-performance eBPF alternative.