Docker 101: Build Container Images
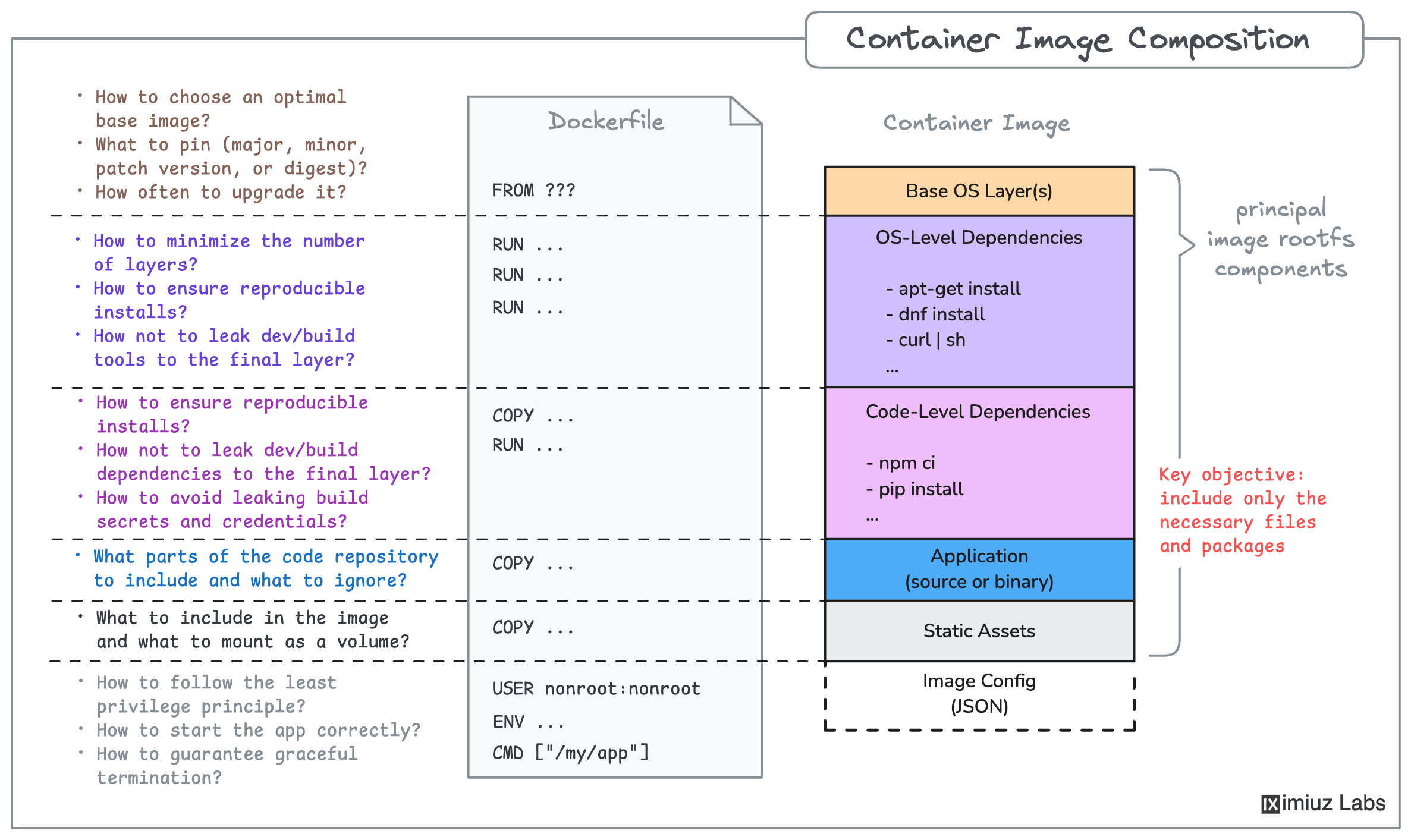
Knowing how to run containers is only half the story - sooner or later, you'll need to package your own applications into container images. This skill path helps you learn Dockerfile authoring from the ground up, starting with the simplest possible image and building up to production-grade multi-stage builds and multi-platform support. You'll learn how to:
- Build and publish a container image to a registry
- Write Dockerfiles using core instructions:
FROM,COPY,RUN, andCMD - Handle application and system-level dependencies in a Dockerfile
- Compile and build applications inside a Dockerfile
- Inspect container image internals (layers, sizes, digests)
- Optimize images with multi-stage builds to produce smaller, cleaner production artifacts
- Use
ENTRYPOINT,ENV,USER,STOPSIGNAL, andARGfor production-ready Dockerfiles - Understand container image internals: layers, configs, manifests, and image indexes
- Build images for other platforms using QEMU emulation, cross-compilation, and remote builders
- Build and push multi-platform container images
By the end of this skill path, you'll be comfortable writing Dockerfiles for real-world applications, understand image internals, and know how to build for any target platform.
Prerequisites
- Linux command-line knowledge
- Familiarity with installing OS packages and tar archiving/unarchiving
- Basic container running skills (see Docker 101: Run and Manage Containers)
Premium Materials
Official Content Pack required
This platform is funded entirely by the community. Please consider supporting iximiuz Labs by upgrading your membership to unlock access to this and all other learning materials in the Official Collection.
Support Development